While receiving the Hoopa gift from the 18th Pokemon movie series, I suddenly felt like hacking into how this entire mystery gift process works.
I looked up on GBATemp and Project Pokemon but interestingly I could not find any technical insights on it. People had pretty much no progress after capturing the encrypted connections.
So, challenge accepted.
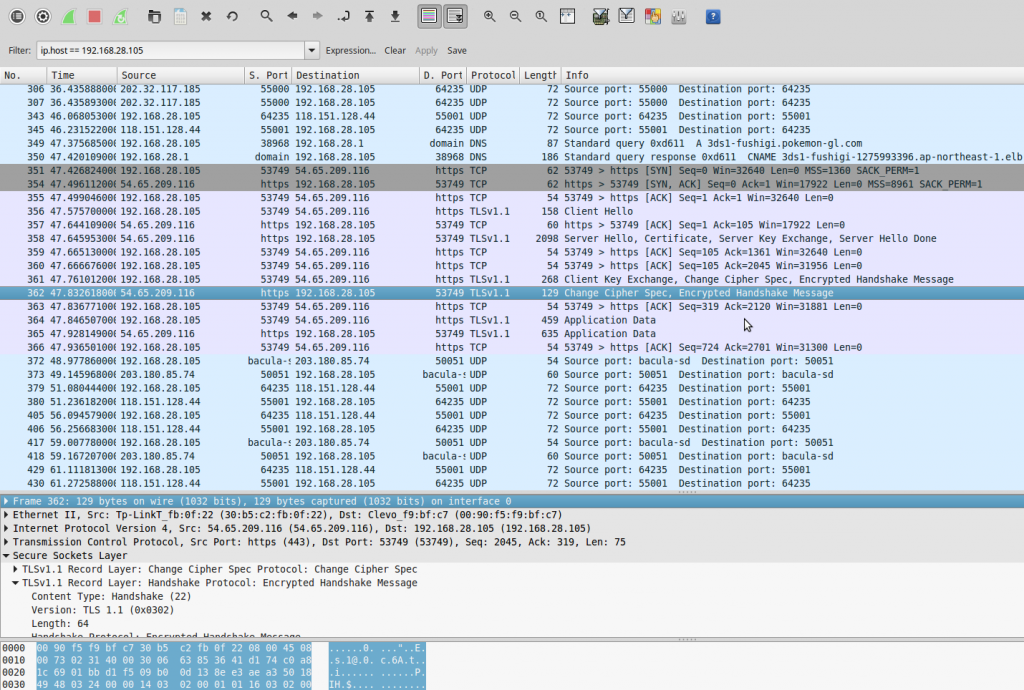
First, I went down to the basics like everyone else; Packet capture.
I used my laptop as a bogus wifi network to capture the packets from the 3DS
The 3DS was communicating with Nintendo servers with SSL as I expected.
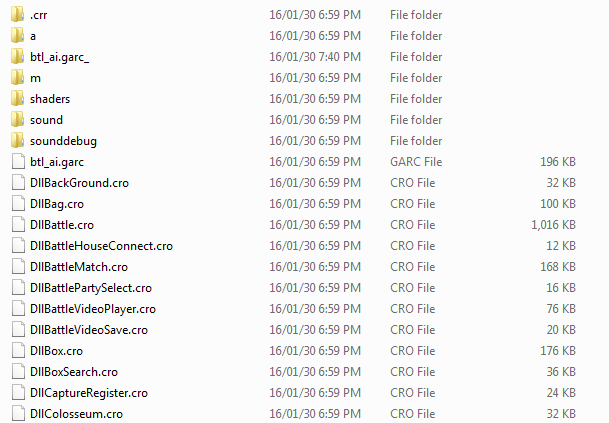
I guess that it might be storing the certificate chain in the game file, as far as I know Wii games store their certificates within the game file.
I wasted a day trying to decompile the rom filesystem and searching for any meaningful information using grep. But eventually I found out that the certificates are not stored in the game file but it is embedded within the firmware SSL module.
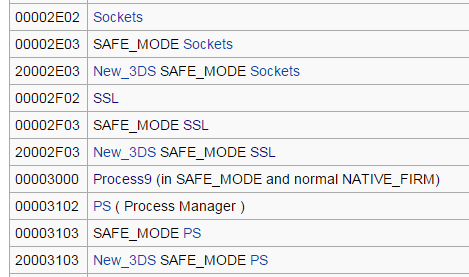
I looked up for the ID of the SSL module and extracted the cia file from nintendo update server.
As all the update cias are encrypted, I needed to decrypt them using a 3DS.
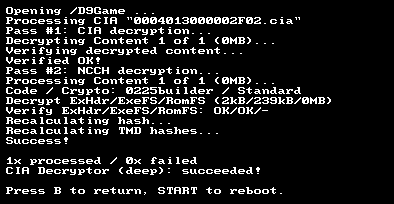
Using Decrypt9, I retrieved the decrypted CIA file.
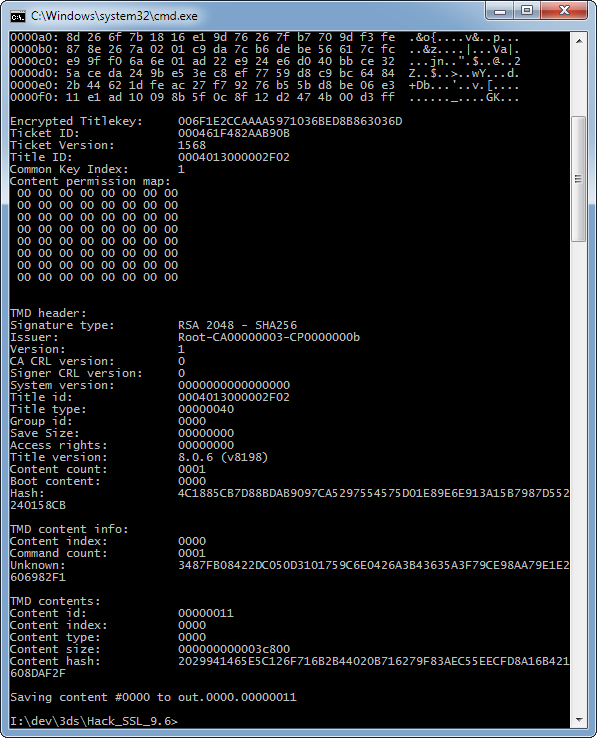
Lets get into the actual data using ctrtool.
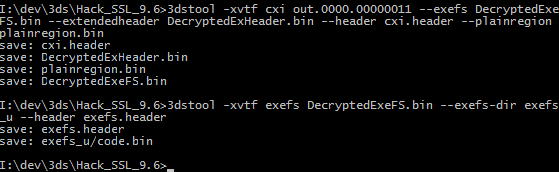
Extracted the CXI portion from the dumped CIA file.
Now we need to get it splitted into proper partition.
I extracted the executable code from the exefs.
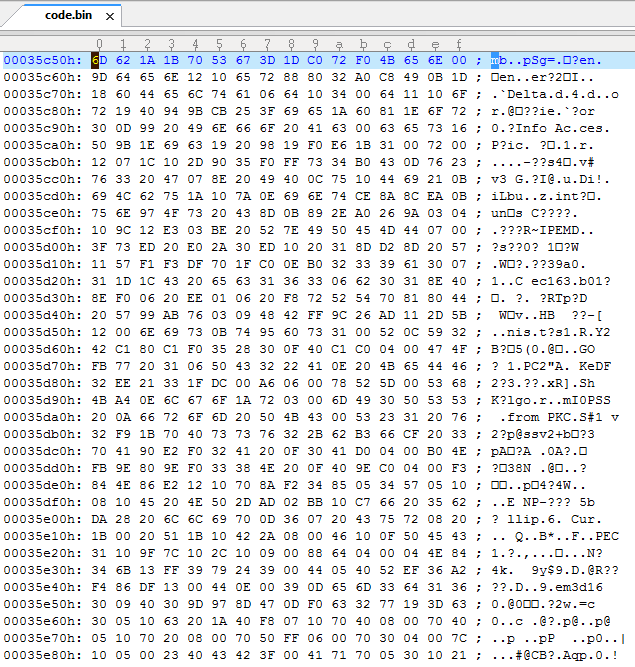
Lets take a look…
It is compressed with reverse LZ77 so lets uncompress it again.
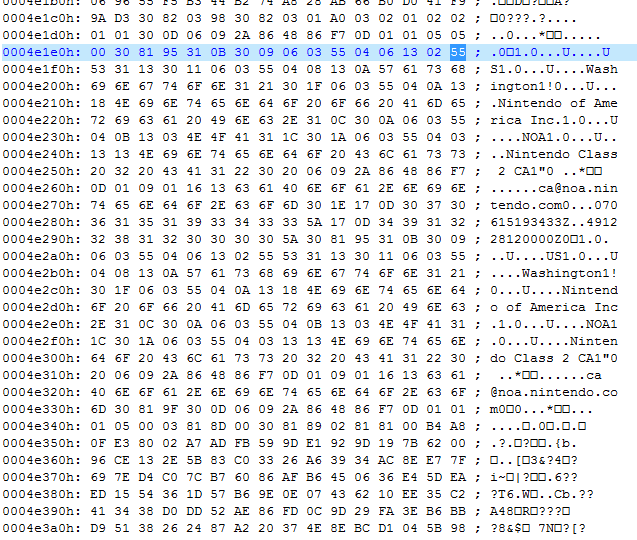
After a bit of skimming I located the actual root certificate used for connection to 3ds-fushigi server.
Thank god Nintendo didn’t use complicated cert chain. As the root certificate is directly used for the communication we replace that and the work here is done.
The format seemed to be DER so I carefully exported the corresponding bytes.
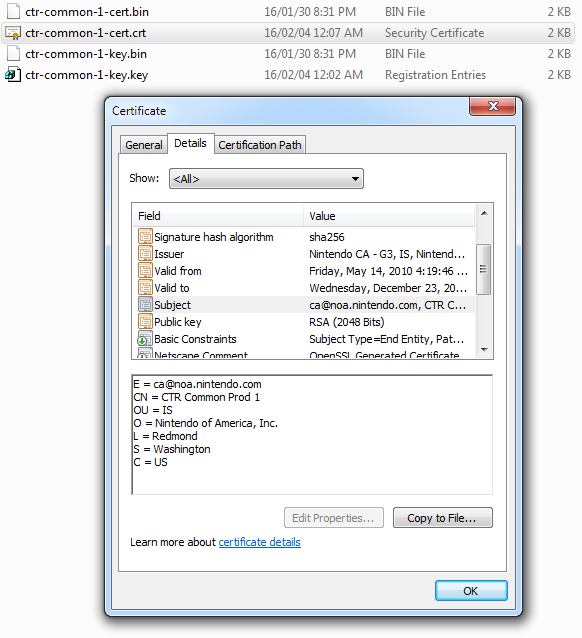
Successfully retrieved the certificate in one shot.
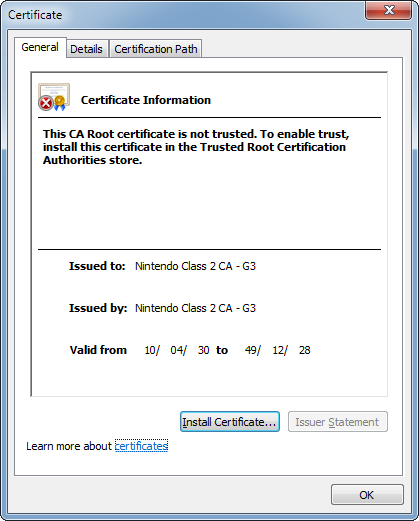
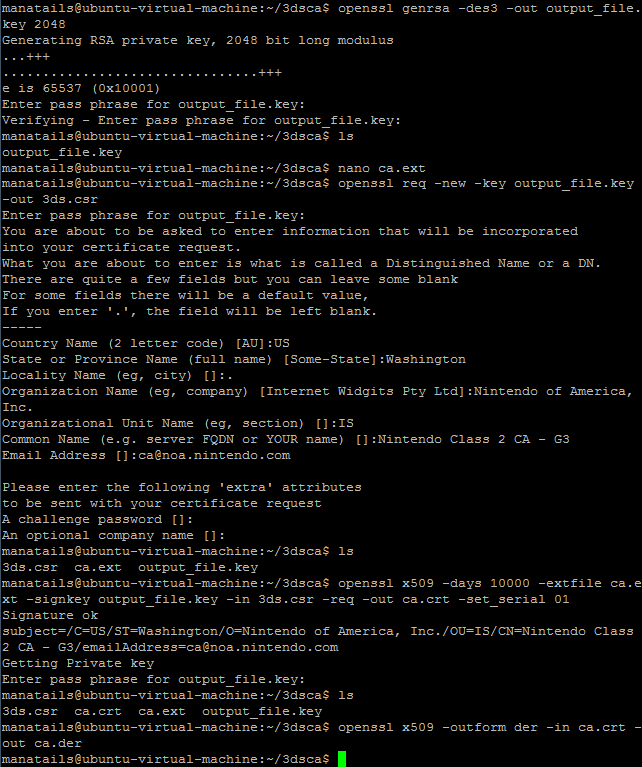
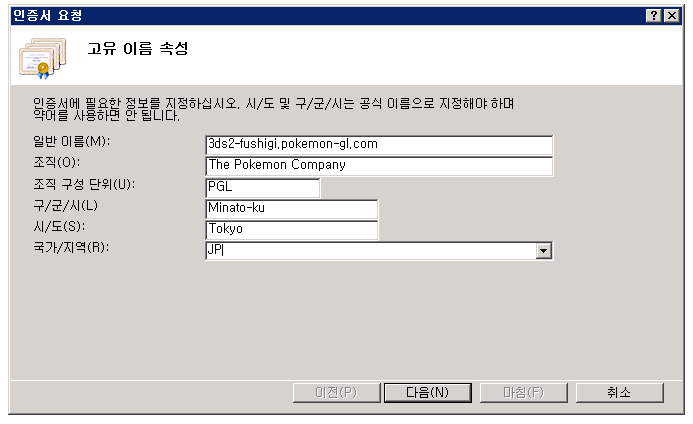
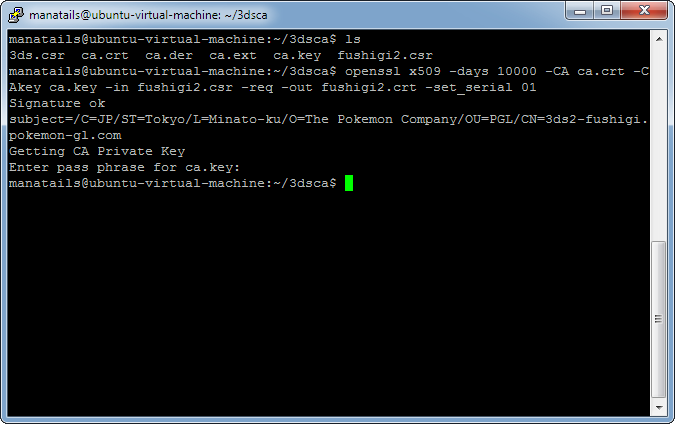
Now lets create a certificate that is almost the same except that it will use MY private key.
Using OpenSSL I created the copy of the certificate, self signed it and converted it to DER format again.
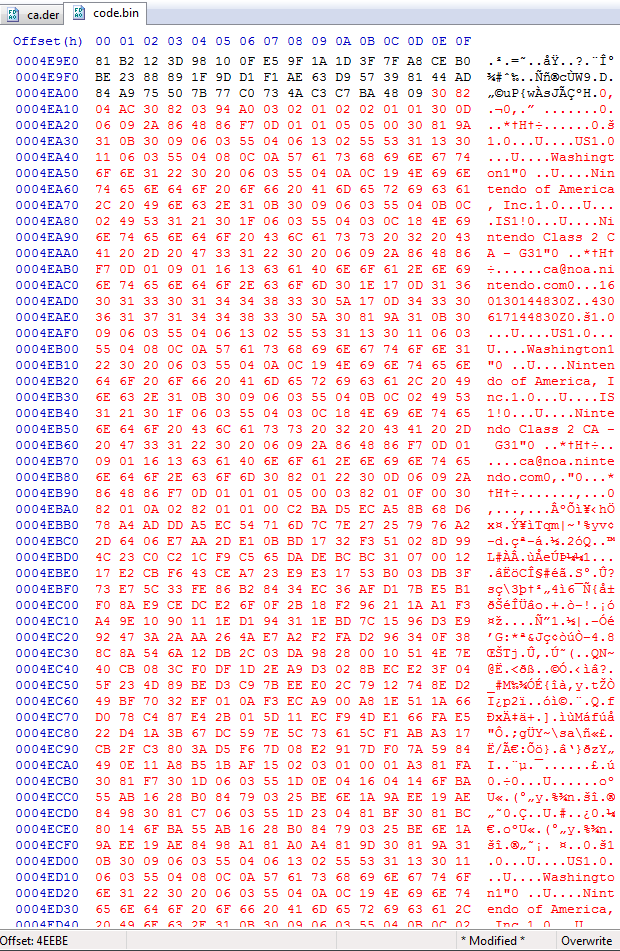
I replaced the certificate in the code binary with the new one then I recompressed the code.bin with reverse LZ77.
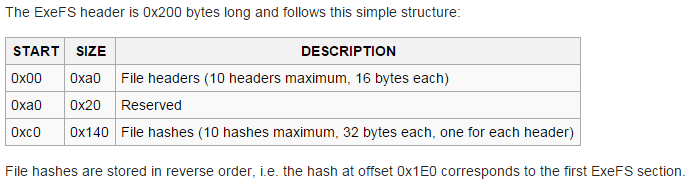
But the header of the exefs requires the hash of the code.bin file, as I could not find any software that does the job for me I ended up patching the hash myself.
Then I redid the entire CIA decompiling process in the reverse order to create the new modified CIA file.
I installed the new CIA file onto the 3DS using devtool but it half bricked the 3DS upon reboot.
This is what a half bricked 3DS looks like. there is no menu on the bottom and it refuses to execute any of the softwares.
Trying to run Camera app using L+R freezes the console.
I wasted another 2 days trying to figure out what is going wrong, then I eventually found out that encrypting the CXI in the CIA file and using a sigpatched firmware could get around the problem.
By the time I worked on this there was no software capable of doing this but now one can use Decrypt9 to encrypt the CXI.
Anyway as the patched certificate is now in position we are moving onto server setup.
I changed the DNS settings of my 3DS and used redirected 3dsX-fushigi.pokemon-gl.com to my server’s IP address.
I created the certificate for secure https using IIS.
Then I started the mystery gift from the 3DS to see what happens.
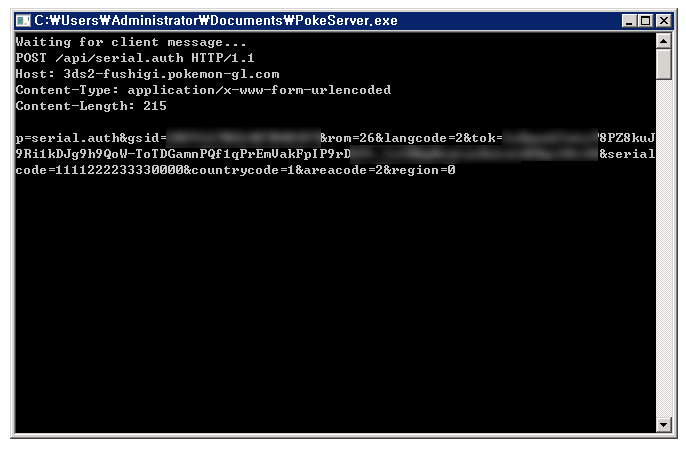
Looking into the log I found that the 3DS was sending a request using a non-standard http format.
2016-02-03 12:07:40 *.*.*.* POST /api/serial.auth – 443 – *.*.*.* – 500 0 64 60
So I coded a secure proxy to dig into the detail.
This is the request sent from the 3DS for validating the gift code with Nintendo servers.
It contains the player’s GameSync ID, language settings, rom type, country code and etc.
Also the gift code in plain format, in this case 1111222233330000.
At this point I thought pretty much everything is over… and I was wrong.
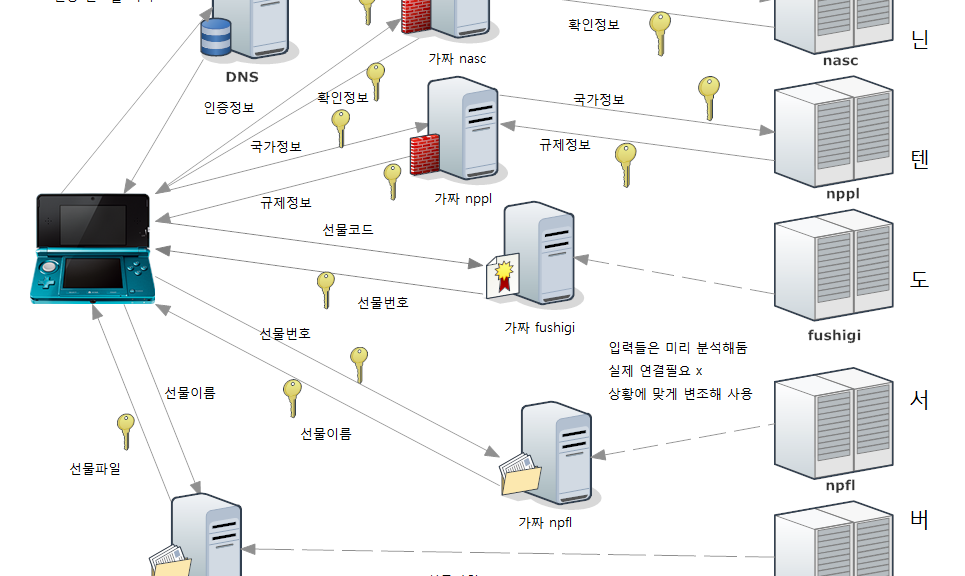
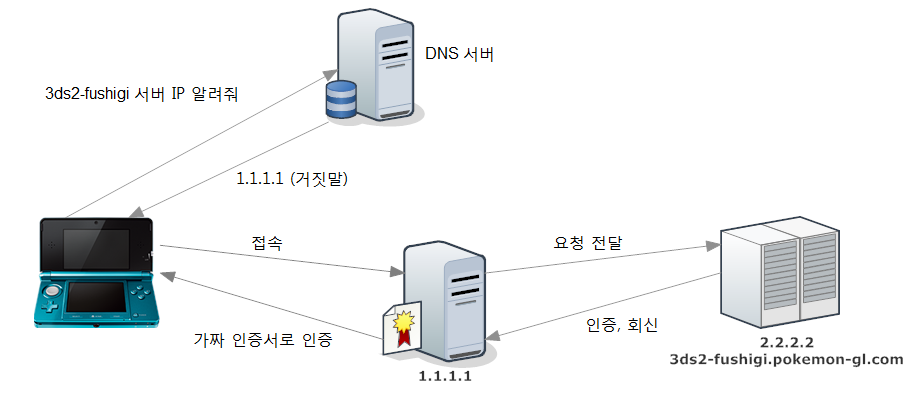
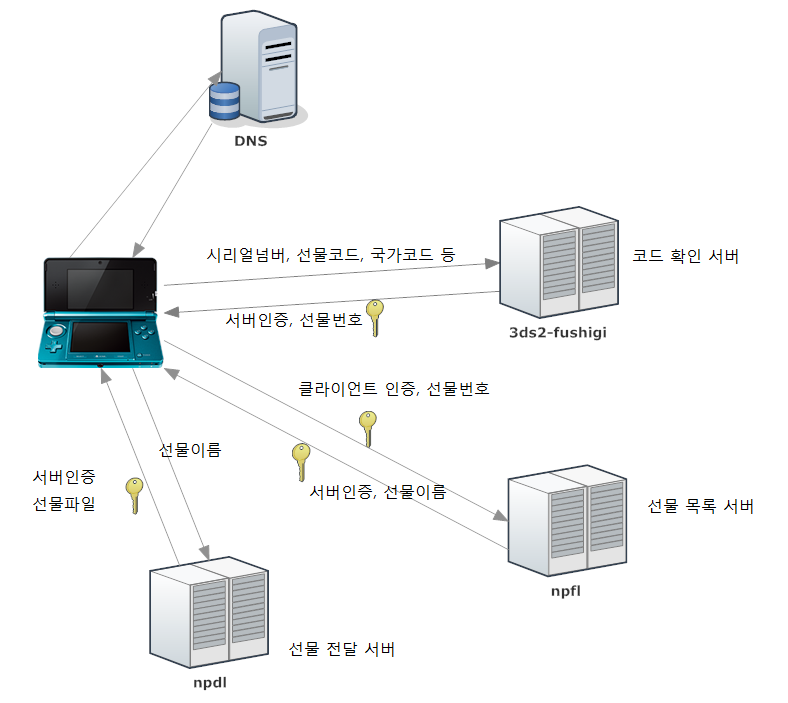
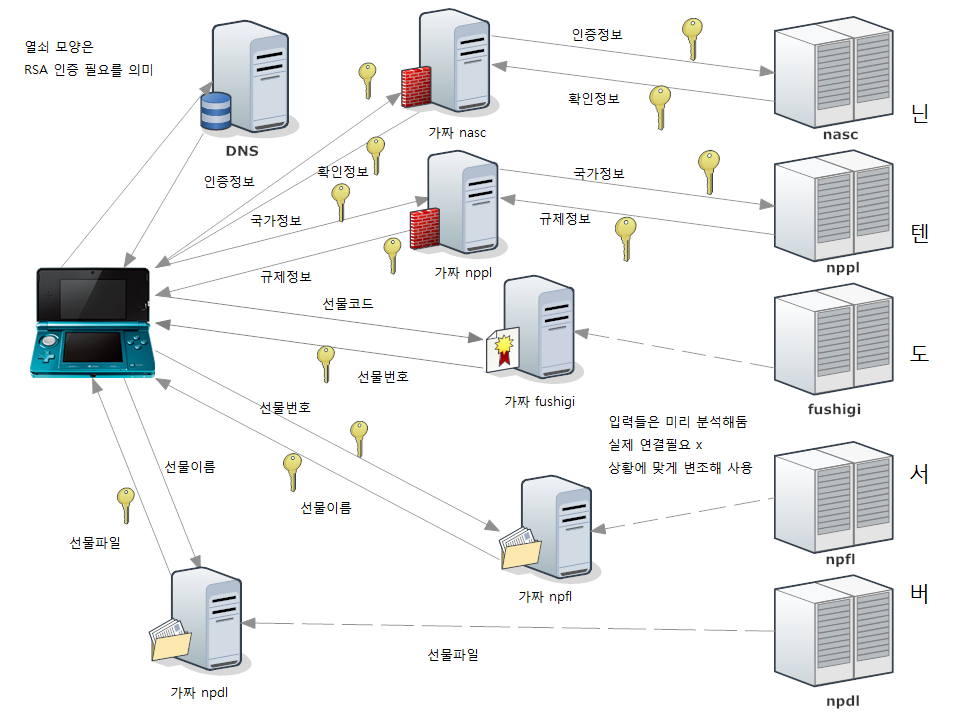
A simple diagram for non-techy users.
I used a rogue DNS to redirect the traffic to my server and my server is behaving as the Man-in-the-Middle.
But strangely the response from the Nintendo server did not contain any information about the gift Pokemon.
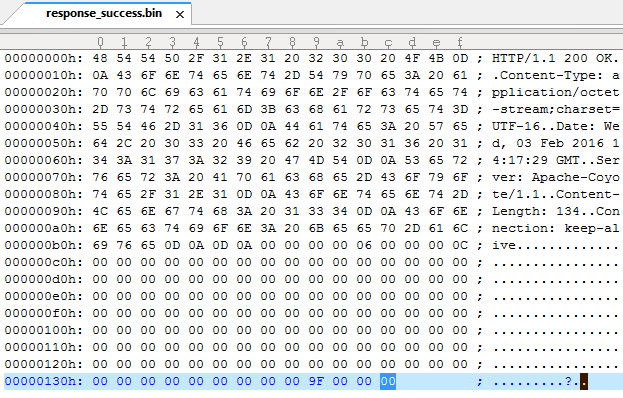
This is the original response from the fushigi server.
I used a couple different working keys for comparison and discovered that it only tells the 3DS if the code is correct or the gift number on successful validation.
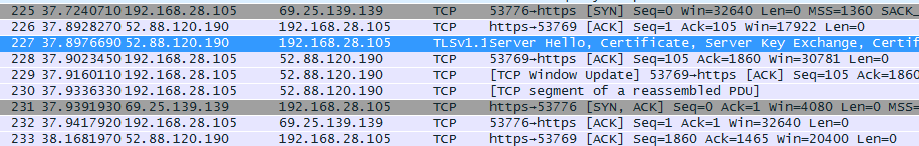
I did the packet capture again to see what it does after getting the response from fushigi server.
After disconnecting from fushigi the 3DS was connecting to npfl.c.app.nintendowifi.net.
But unlike fushigi, npfl server requires client authentication using a clientside certificate.
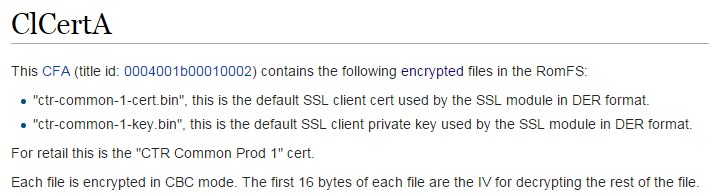
The client SSL certificate resides in a module called ClCertA
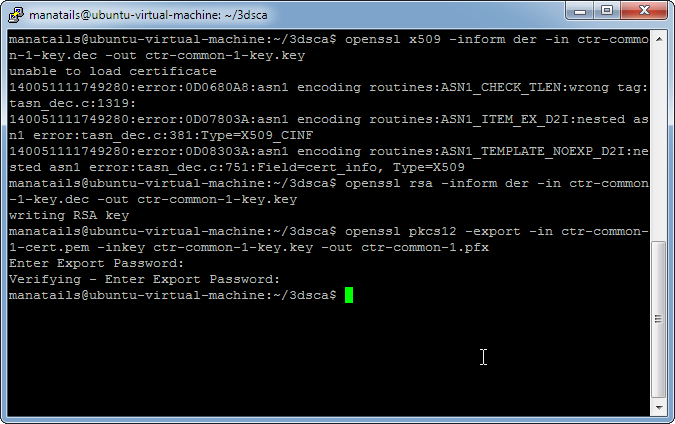
Extracting the certificate is done the same way as extracting the root certificate. But unlike the latter the client certificate is encrypted with AES-CBC, but thankfully we have a tool for that purpose.
Successfully extracted the certificate and key from the module
let’s convert the certificate into a more PC-friendly format.
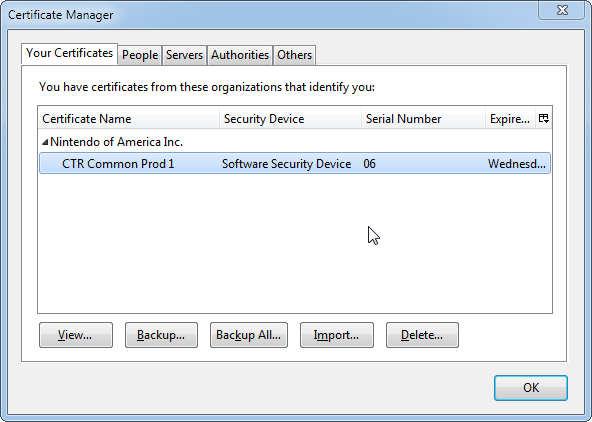
Importing the certificate into the browser now enables us to impersonate as legit nintendo 3DS’s
Now let’s see what the server has to show us.
I see that the NPFL server holds the list of available gifts.
If given a gift number it will output the corresponding gift name for that number, if no input is given it shows all the available gifts.
File names are pretty much self-explanatory, although there are a couple of confusing names like M18KO_A, M18KO_HU. Which I guess means Arceus and Hoopa for the 18th Pokemon movie in Korean region.
One interesting thing to note is that when a 3DS connects to this server, it displays “Searching for gift…” message. It is _literally_ doing it.
If NPDL server gives a response and 3DS does find a gift, it will then connect to NPDL server to download the actual gift file.
To summarize, The process is like the diagram above.
I coded a program for simulating each of the servers, but I discovered that NPFL server is using a different certificate chain than others. It is authenticated using Nintendo G3 root certificate as opposed to other servers using Nintendo Class 2 cert. I can also replace the G3 certificate in the same way I did for Class 2, but as G3 certificate is also used for connecting to NASC and NPPL server, which is used to authenticate the nintendo 3ds and the cartridge itself everytime it tries to connect to the internet. I couldn’t figure out a way to emulate those servers due to their cryptic response format, so I ended up coding a secure proxy server that redirects all the information to the legit servers.
So this is the final diagram.
fushigi, npfl and npdl servers are accessed consecutively, so there is no problem running everything on a single server. But nppl and nasc servers are accessed randomly during connection, somethimes even simultaneously so they must be ran on different machines.
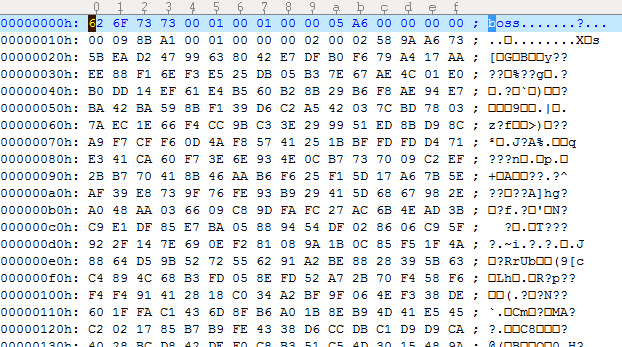
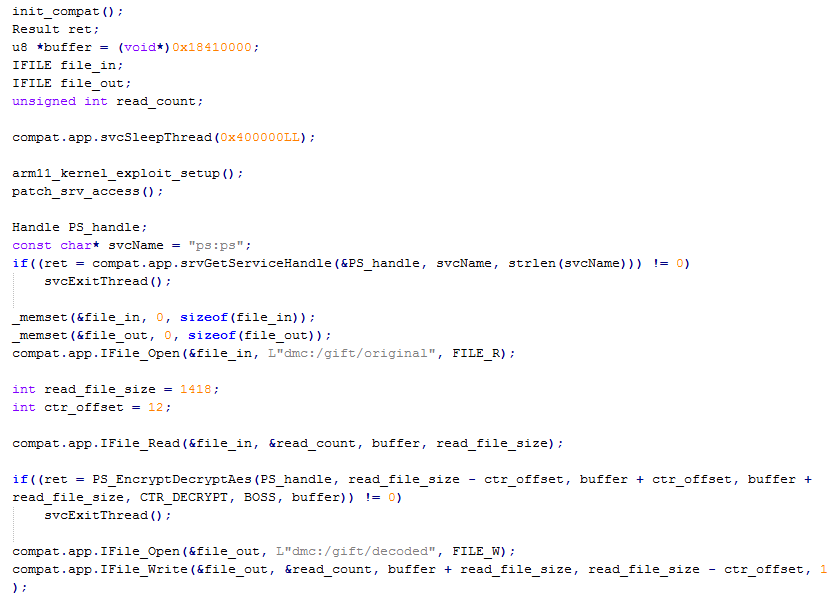
Anyway now I proceed to analyzing the output of the npdl server.
Despite so many steps it is still encrypted…
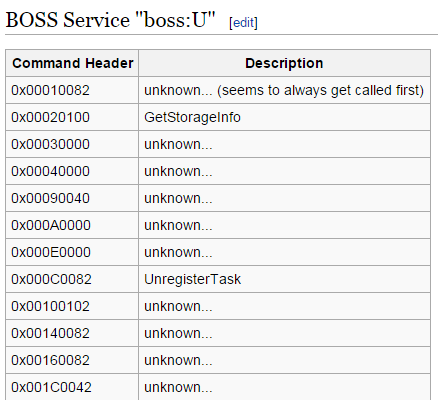
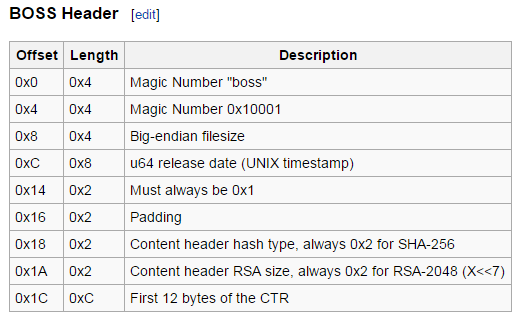
It is the BOSS format used in SpotPass, but to this date nobody bothered to document anything about the service.
But thankfully the specs for the header are documented, I coded a boss format decrypter from the information.
It is encrypted almost the same way as the client certificate execpt that it used AES-CTR and different set of private key. I coded another homebrew that is capable of decrypting AES-CTR from the raw data. the starting bytes of the CTR is the 12 bytes following the header plus 1 in big endian, so for this file the starting bytes will be 58 9A A6 73 5B EA D2 47 99 63 80 42 E7 01 00 00 00.
Presto! the gift is successfully decrypted. Although the actual format of the gift I will investigate later.
Now finally we can give ourselves a gift…
This is Amaura which my servers are gifting to my nintendo 3DS, with an arbitary gift code of MANATEE.
But as the gift file itself is also signed by nintendo, I guess there will be more stuff to be done before we can start creating our own giveaway pokemon.
The source code of the server emulators and AES-CTR decryptor will be released soon.




It’s interesting to see how some of the events that has ended, are still on the server (Example Emboar and Arceus).
Since they can be shown on the server, I assume they also can be extracted.
It is interesting to note that I don’t seem to see the “Local Wireless” distributed events on the server.
Hence, I would assume that local events are distributed through separate hardware that doesn’t authenticate with the server.
Is it presumptuous to think that it will be easier to create homebrew to run on the 3DS to do the distributions, base on the above point?
Anyhow, great job, was really surprised to see someone get this working! 😀
Well, I have been making snapshots of npfl server responses everytime I felt like doing it, and I found that not all gifts are kept on the server. Some get removed as well, for example the server does not give you anything about 18th Movie Hoopa and Arceus now. Although the actual file seems to be kept in npdl server it is no longer accessible, inputting the names of expired gifts returns a null response. It is clearly different from when you request a nonexistant gift where the server returns 404 NOT FOUND, anyway it seems that the only way to secure all the gifts is to regularly query npfl and npdl servers and cache their responses.
As I am not a pro pokemon player I don’t know much about the local wireless distribution, but I guess that the procedure will be pretty similar and it will require doing MITM at some point, annoying stuff.
I think maybe IR transmission will be easier to implement provided with proper IR debugging hardware, but that is a rogue assumption.
Well, they probably archive it, to use it for comparison sake in the future, or something.
Previous generations for distribution cartridges, it was tied to the date of the DS, for when it’ll become unavailable for distribution, so it could be programmed to be unavailable based on server clock.
I’m no pro too, and I’ve haven’t personally seen the “black box” that others refer to, as most events I get here are serial code events, but I’ll reckon it isn’t easy.
We do have some of the more recent full events, including the distribution info and checksum.
So far it seems only Korean events are distributed via IR, so I’ve haven’t seen what its like too.
Hey,
Based on your image (24.png), using the name in the image,
one is able to download the full cards (encrypted) onto one’s computer (by pasting the names behind a certain link).
Is it possible to discuss some of this over e-mail?
Downloading the encrypted cards and decrypting it is not a problem as long as the servers have them online. I can do it if there are people who want them. It is just that I was too lazy to code a script that does the job automatically…
If you would like to contact me my email is manatails at mananet dot net
Hi. Will you release the source code soon? I’m interested on seeing how you managed to fake Ninty’s servers
Hi! Do you still intend to release the code?
Hi,
I was so glad to see your post. But when I try to follow your steps, I encountered some problem. How did you dump CIA files from the 3DS, and how did you install a modified certificate file onto the 3DS?
For dumping the CIA files I just used the files from online update server. Installing the modified certificate is actually done onto a custom EmuNAND firmware with sigcheck disabled.
Thank you for the reply.
Can you show me in detail how you actually installed the modified certificate? I’m new about the EmuNAND. Thank you !
“It is compressed with reverse LZ77 so lets uncompress it again.”
Could you tell me what tool did you use to uncompress the code.bin?
3dstool -z –file code.bin
Manatails can you please send all programes and certificates or the source code! Cause i am planning opening up my own Nintendo 3DS Mystery Gift Network! Please send a download link to : trille@trilleplay.net
And Dude you are Truly Awesome Reverse Engineer!
Very interesting, does this require any self singed certificates to be installed on the 3ds? also would you mind posting the server code to github?
Thanks in advance,
Kyr
The original post already includes the process for installing the self signed certificates on the 3DS.
I decided not to publish the server code but it is not that difficult to code your own… most comms are merely transferring files through HTTP
Hello, I have wanted to recreate all of the Gen 6 mystery gifts but I have no idea what any of this is. Do you know anywhere I can learn all this stuff.
It takes many years of experience. You won’t be able to learn it in one place.
So release it wtf 😭
like all stupids you only do to look more cool, because you never relaeased a shit even you pomised.
저도 오루알사에서 배포받아보고 싶습니다…
Do you ever plan to release the code, and do you plan on doing this with gen 7 as well?
안녕하세요 NeckDoria 라고 합니다.
8월 4일에 웹 3.0 국회에서 다음주 8.4일 날, 저희 지역구 의원[민병덕의원님] … 웹 3 생태계 혁신과 디지털 자산의 미래
라는 주제로 25년 8월 4일(월) 오후 2시 국회 의원회관(2층,제1소회의실) 선생님의 글을 일부 인용해서, 이런 사례가 있다라는 주제로 언급을 할까 하는데 괜찮으실까요?
저는 인증 방식의 변경이 11월 15일 2015년에, 왜 이렇게 역사적 흐름이 흘러나왔나 그 부분에 중점을 두려고 합니다. 선생님의 공학적인 닌텐도 선물 서버 커스텀 구현 방식은 순수하게 선생님이 구현하신거라서, 닌텐도 의 라이브러리를 참고하셔서, 간단하게만 소개하고, 지나가도 될까요? 메일 다시 주시면 neckdoria@naver.com으로 주시면, 제가 인쇄해가지고 가고, 그럴 거를 준비해서 논문처럼 만들어볼 생각인데,
주제는 지금은 포켓몬 시대의 웹 3.0인 가 웹2.0인가 웹 2.5인가 주제입니다.
부가적으로 인증방식의 역사와 관련해서 언급하려고 하며,
양커뮤니티의 평가가 엇갈릴 수는 있는데,
잘 안될 것 같습니다. 그냥 안하려고요.
사이버로 참여해서 들을 수 있으면 들으려고요.
보안 상 경함이 추후에 게임에 영향을 끼칠 수 있는 영향이라는 주제로 글을 쓰려고 했는데,
쉽지가 안네요.